Eigercode Tools for the IT-Admin
We make IT more fun, more flexible, and more independent
UVIT
A full fledged Device Management
- Mobile device management for Windows, macOS, Linux and iOS
- Connect your identity provider or use ours
- Software deployment for Windows, macOS, Linux and iOS
- Reliable and up to date statistics and insights
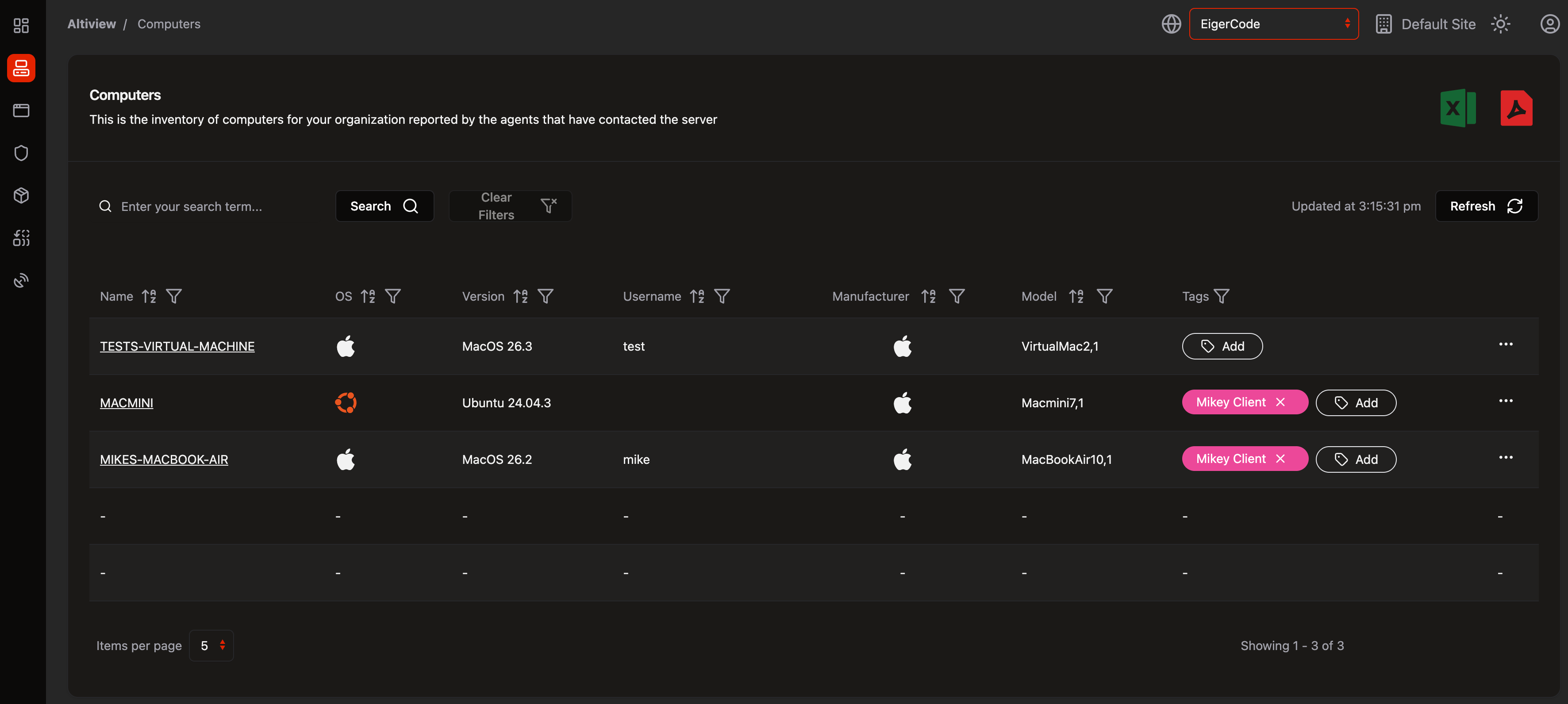
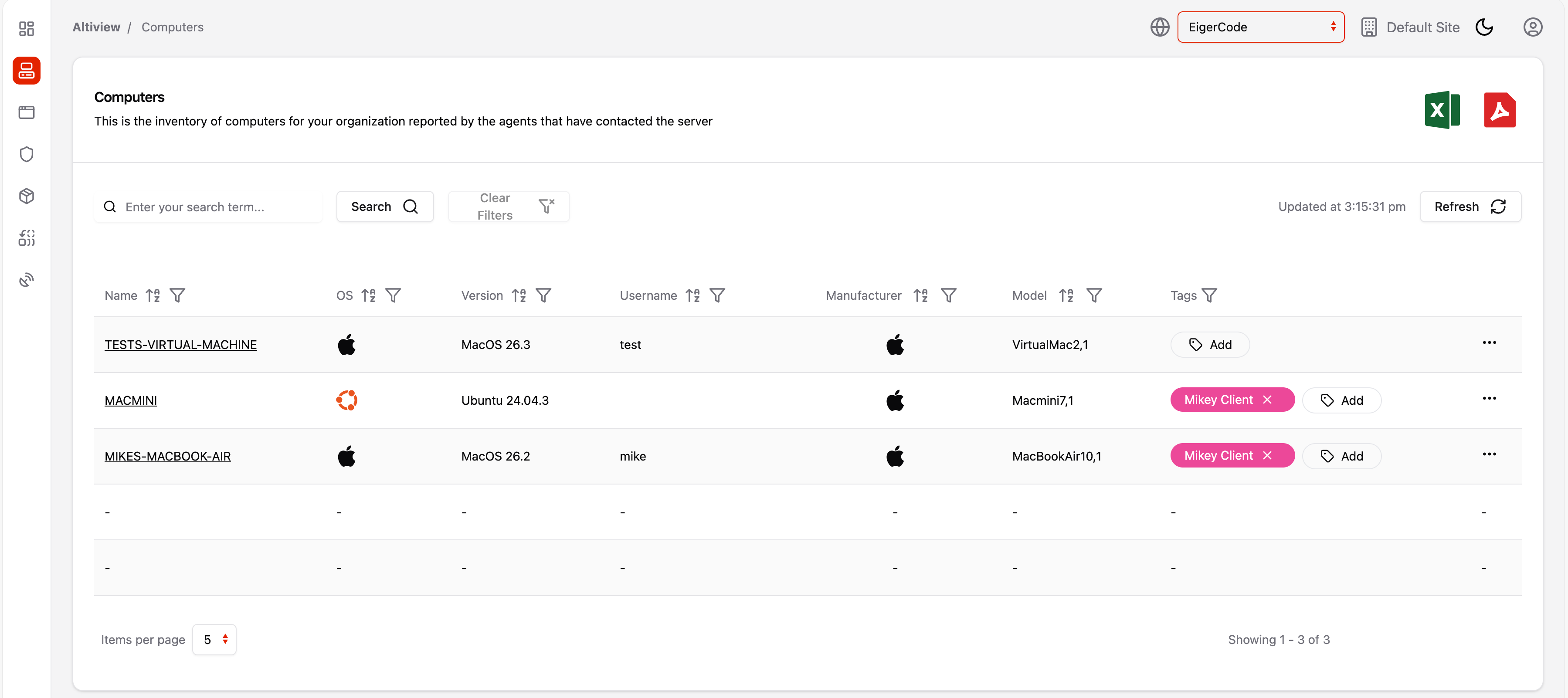
Don't worry about the OS
Manage all your devices from a single dashboard, whether they're running Windows, macOS, Linux or iOS. No need to juggle multiple tools or learn different interfaces—our unified platform works seamlessly across every operating system your team uses, giving you complete visibility and control regardless of what your employees prefer to work on.
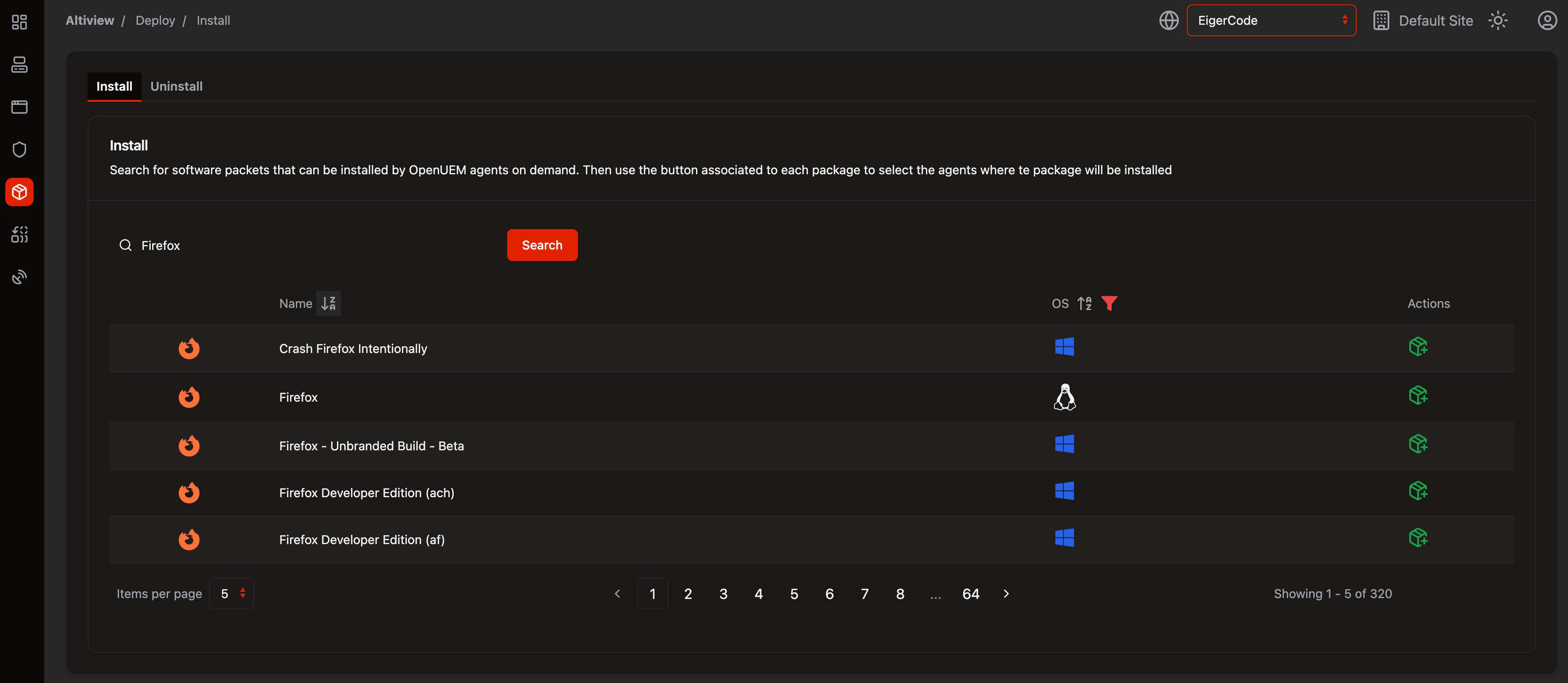
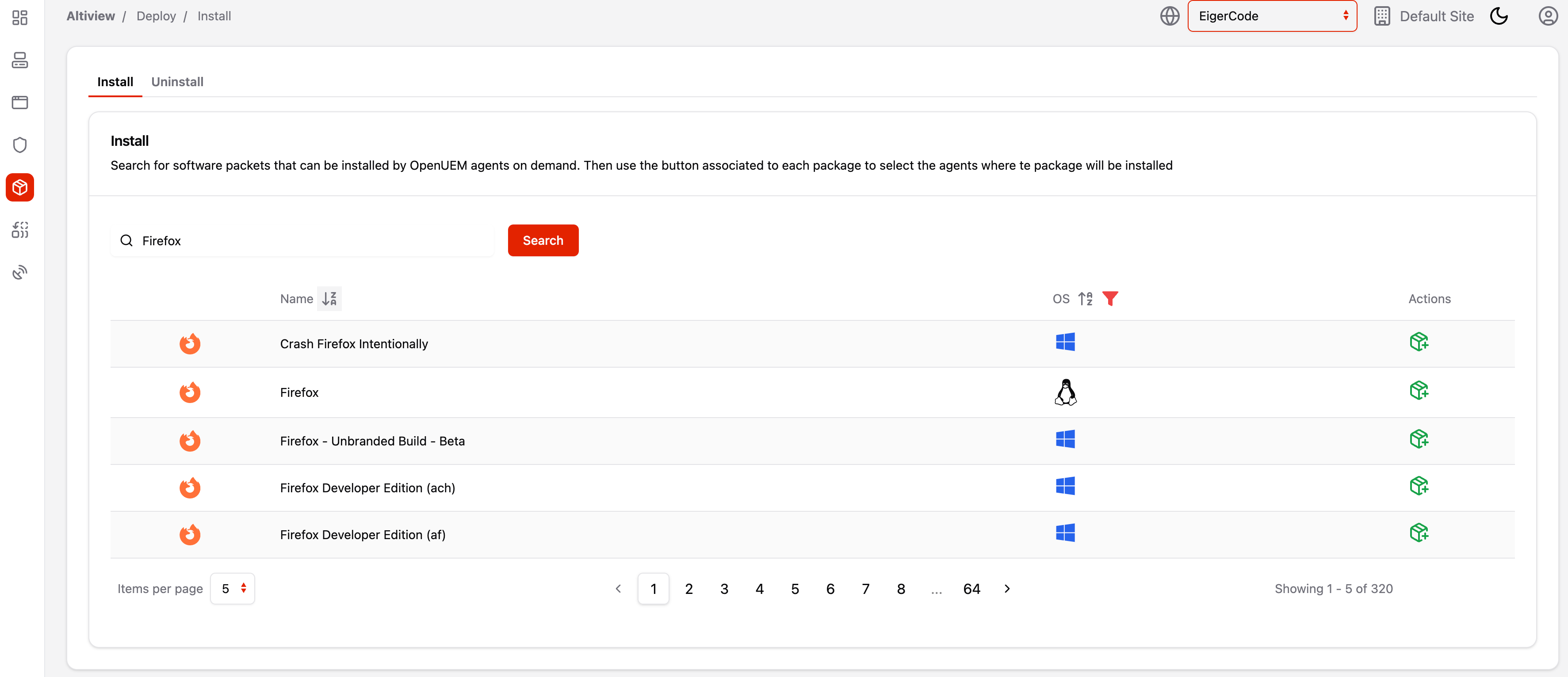
Deploy Apps in Seconds, Not Hours
Push applications to any device across your fleet with just a few clicks. Just choose an App from our catalogue or upload your own. Target specific groups or individual machines, and track installation status in real-time. Whether you're rolling out new tools, our streamlined deployment process eliminates the manual work and ensures every device gets what it needs when it needs it. It even installs your favourite brew package.
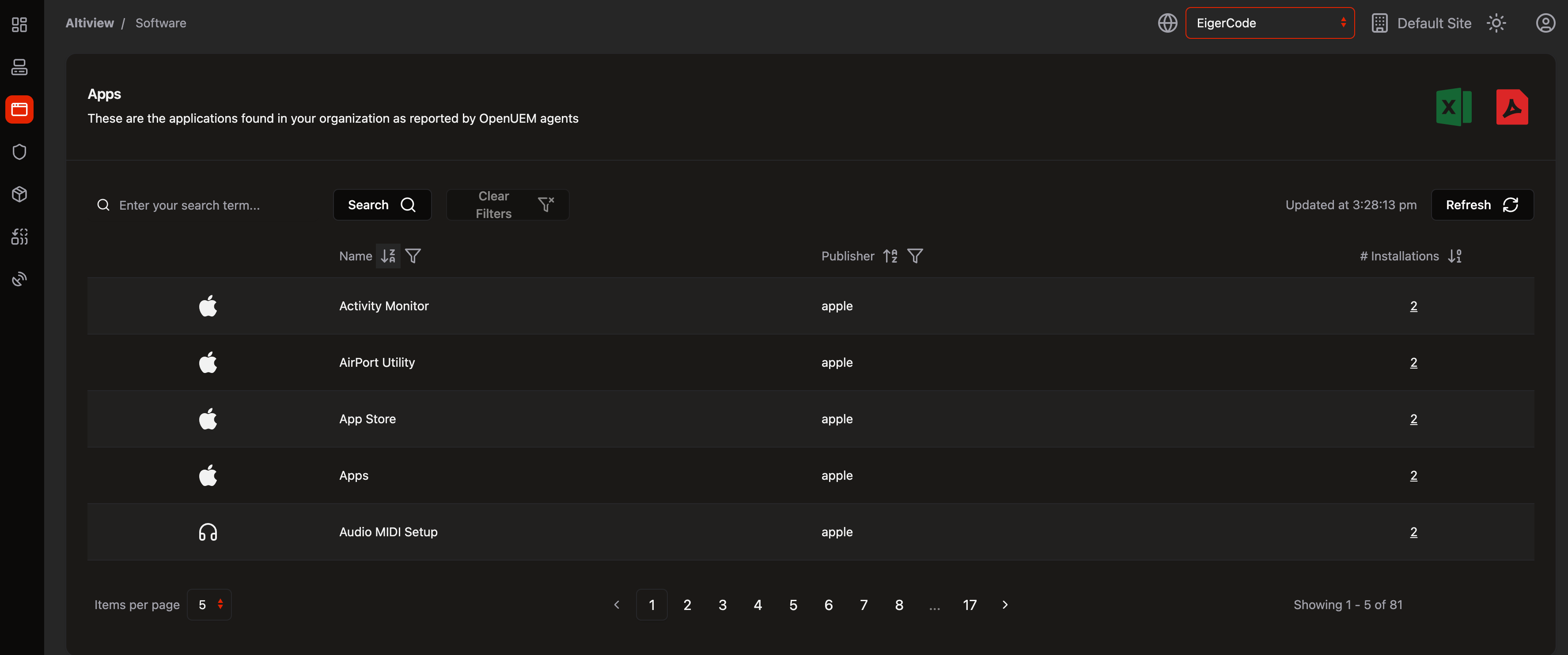
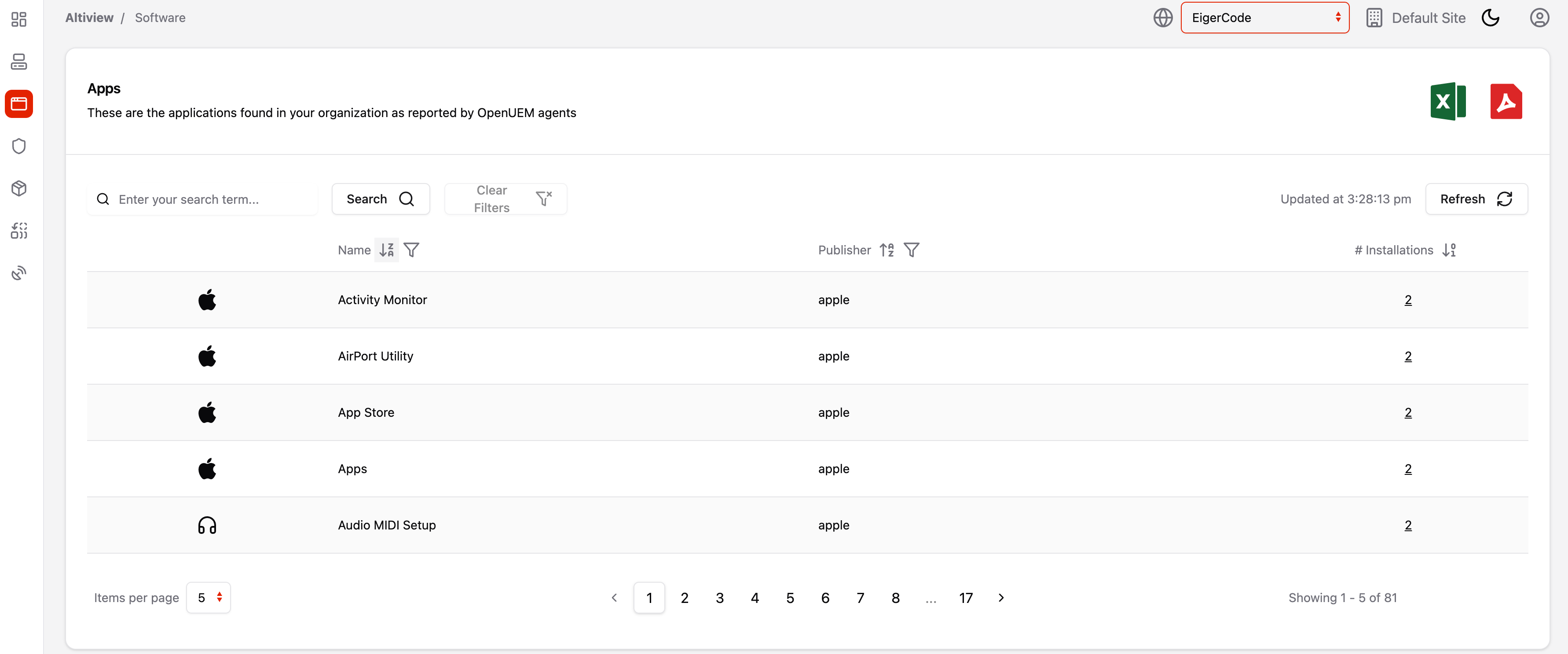
Know Exactly What's Running Where
Get a complete inventory of every application installed across your organization. See which apps are deployed on which devices, track license usage, identify unauthorized software, and spot version inconsistencies at a glance. Our comprehensive monitoring gives you the visibility you need to maintain compliance, optimize software spending, and ensure your fleet is running exactly what it should be.
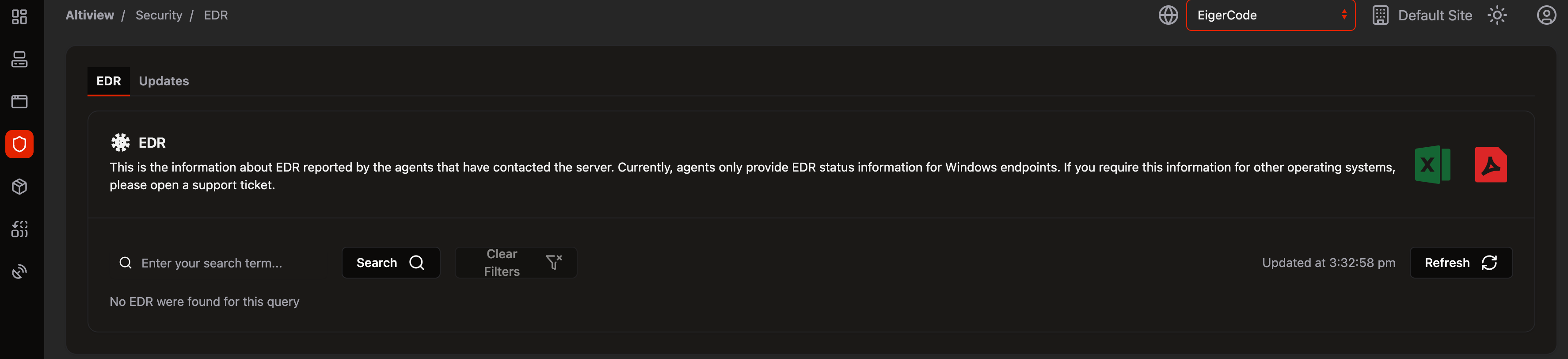
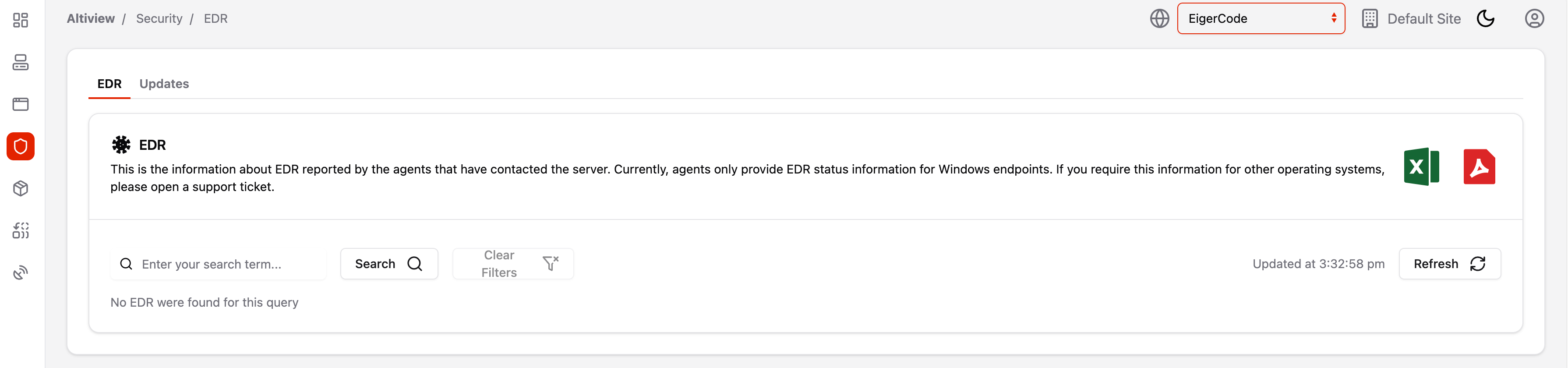
Built-In Threat Protection That Never Sleeps
Protect your devices with enterprise-grade endpoint detection and response built right into your management platform. Our EDR continuously monitors for malicious activity, detects threats in real-time, and responds automatically to contain risks before they spread. No separate security tool needed—get comprehensive protection against malware, ransomware, and suspicious behavior while maintaining complete visibility into your security posture across every endpoint.
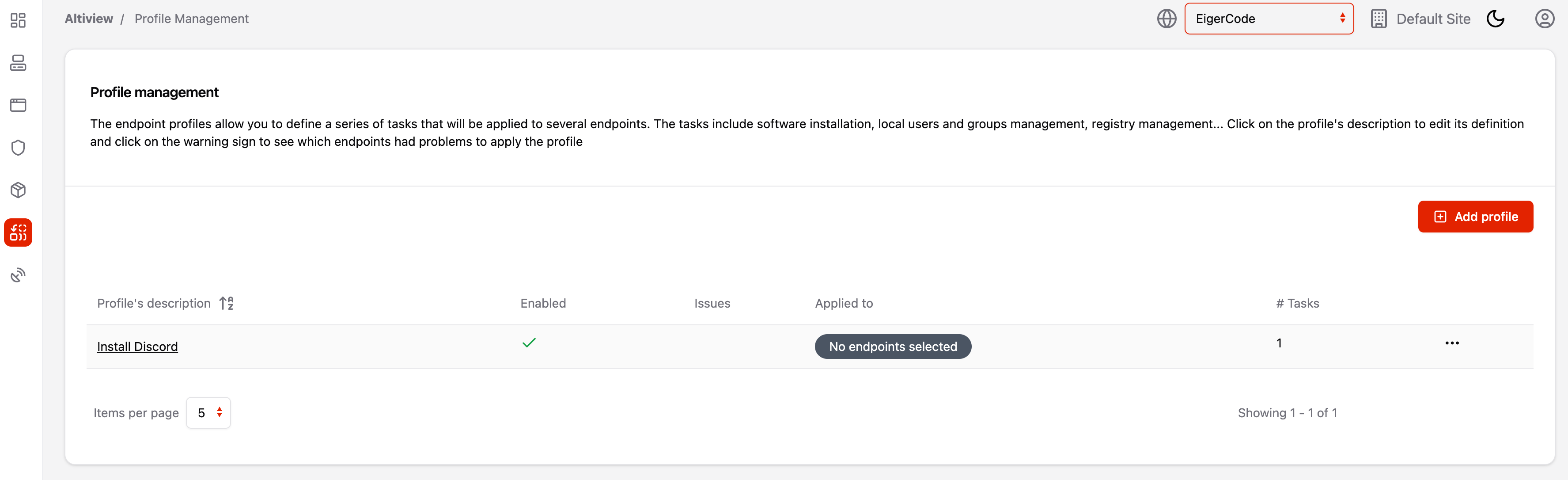
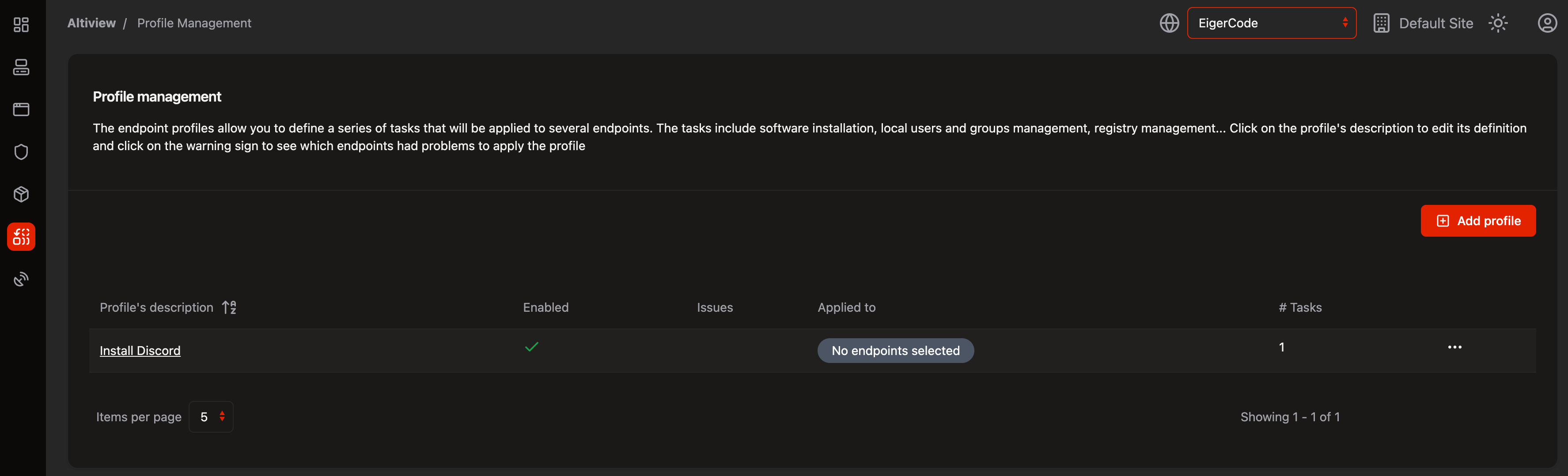
Configure Once, Deploy Everywhere
Standardize device configurations across your organization with centralized profile and settings management. Create custom profiles for different teams or roles, push security policies, configure network settings, and enforce compliance requirements—all from one place. Whether you need to update Wi-Fi credentials for hundreds of devices or lock down specific settings for security, deploy your configurations instantly and ensure consistency across your entire fleet.